You’ve probably noticed recently the DDoS attacks on ABN-Amro, ING, Rabobank, and the Dutch Tax Authority. However, DDoS attacks are nothing new and are often a daily occurrence for many companies with extensive IT environments, including ourselves.
What are DDoS attacks, what are the consequences of a DDoS attack, what are the common motives behind them, and how can you prevent or defend against them?
What is a DDoS attack?
DDoS stands for Distributed Denial of Service. The usual goal of a DDoS attack is to make a website or service unavailable by overloading the bandwidth or monopolizing the resources of a server/infrastructure until they are exhausted. This can be compared to a store entrance. Normally, about 20 visitors per minute can enter easily, but if suddenly 20,000 visitors try to get in per minute, within a few seconds, the line outside becomes so long that, practically speaking, no one can get in anymore.
Botnet
DDoS attacks are typically carried out using a botnet, which is a (very large) group of computers and servers controlled by an attacker to execute commands. These are often computers and servers belonging to innocent users who have been infected with a virus or hacked. A botnet can automatically send large amounts of data (requests) simultaneously from multiple locations on the internet to the target. This continues until the target can no longer handle the traffic and becomes unreachable.
Because a botnet usually consists of infected computers and servers, and the actual attack rarely comes directly from the attacker’s computer—with many intermediaries involved—it is virtually impossible to determine who is behind the attack.
What are the consequences of a DDoS attack?
The direct effects of a DDoS attack are usually that a website or service becomes unavailable. However, the consequences are often significant—think of loss of revenue (for example, a webshop unable to sell), employees unable to work (such as an intranet that’s down), reputational damage (being unreachable generates distrust), and so on. As a result, DDoS attacks often have a huge impact and there can be many motives for an attacker to carry out a DDoS attack.
The damage is rarely recoverable, as the actual attacker can often not be traced, not even by the police, the justice department, or other authorities.
Motives behind a DDoS attack
Whereas in the past, conducting an attack took a lot of time, knowledge, and effort, nowadays it can be done very quickly and easily. There are many places on the internet where you can literally buy an attack for just a few euros. You simply choose the target, the duration of the attack, and the amount of traffic to be generated, then complete the payment. It’s arranged within minutes and requires little to no technical knowledge. These are often referred to as hacker attacks, but in reality, DDoS attacks are rarely carried out by hackers and are more commonly the work of resentful individuals, groups, or criminals.
Revenge or harassment
Due to the ease and anonymity with which attacks can now be launched, there does not always have to be a strong motive. The so-called ‘revenge or harassment’ DDoS attacks occur frequently, for example a student wanting to take down his school’s website, a dissatisfied customer targeting a particular company’s services, an organization wanting to damage its competitors, or a feud between certain groups, associations, individuals, gamers, etc. These attacks are usually not extremely large, not very complex, and short-lived.
Extortion
If revenge or harassment isn’t the motive, it’s usually extortion. A criminal individual or group announces an attack in advance and offers the possibility to ‘buy off’ the attack. Below is an example of such a threat.
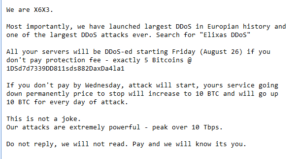
In this case, the group announces who they are, what they have “achieved” in the past, and what will happen if you do not comply with their demands. They demand money in the form of Bitcoins and, if payment is not made, the attack will commence, with the price increasing each day until the demand is met. It is not unlikely that a similar scenario played out with the banks that came under attack.
Indirect hacking attempt
A final motive may be to take down a security system or to use deception to distract attention from the real goal/hack. Only in this case is there an actual hack (or attempt). This method is usually far-fetched. There must already be another security vulnerability, and the hacker must act very quickly and usually possess highly specialized knowledge. This is also assuming that a DDoS distraction is even effective, or that disabling one security system is enough to penetrate deep enough to do anything.
So there is no direct danger of a hacker gaining unauthorized access to secret or sensitive data through a DDoS attack. Even in the recent DDoS attacks on the banks, there was probably never any danger to the safety of financial data. In such environments, there are generally multiple security systems in place alongside and on top of each other.
Preventing and defending against DDoS attacks
A DDoS attack can never be completely prevented and never be completely defended against. However, there are measures you can take to reduce the risk of DDoS attacks and defend against attacks as best as possible to minimize their impact.
Clean network
There is a clear target group with an increased risk of DDoS attacks. By not allowing this target group into a network, or by separating them from other users’ networks, you can reduce both the risk and the impact. Groups with a higher risk of DDoS attacks include, for example, game servers, discussion forums, and websites/organizations with political or ideological positions.
Rate limiting, capacity, and optimization
There are also many technical methods to defend against and reduce the impact of an attack. Small and medium-sized attacks can often be repelled by having sufficient capacity and applying ‘rate limiting.’ With rate limiting, if a certain number of requests is exceeded, subsequent requests are automatically blocked. Good configuration and optimization at all levels also ensure that each request consumes as few resources as possible, allowing more requests to be handled before problems arise.
The National Anti-DDoS Scrubbing Center
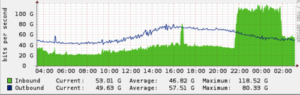
Large-scale attacks are often countered with specialized equipment and large allocations of resources. Dutch internet providers can join the National Anti-DDoS Scrubbing Center (NaWas), and Shock Media also utilizes NaWas. This means that when under a DDoS attack, it is possible to deflect the attack by routing traffic through the ‘scrubber’. The scrubber will ‘clean’ (filter) the traffic and then only send the ‘clean’ traffic onward. DDoS attacks are becoming larger, more complex, and more specialized. This means there is an ongoing ‘arms race’ between attackers and those developing the initiatives, equipment, and capacity to repel DDoS attacks. Completely preventing and repelling such attacks may never be fully possible, but fortunately, development is also ongoing on the good guys’ side.

Do not negotiate!
Someone threatening with a DDoS? Or are you already under attack? Never give in to the demands of an attacker! No response is the best response. Most of the time, it ends at just threats. The actual DDoS is never carried out or is easily repelled. If you respond, they at least know you’re aware of their demands. This makes an attack more likely. If you even go so far as to meet the demands or pay to prevent a DDoS, then criminals know you are susceptible to blackmail. Chances are a new threat with even higher demands will follow very soon.
So what can you do?
Naturally, we always advise filing a report with the police and, if necessary, notifying the National Cyber Security Center. Unfortunately, it is a fact that attacks with little impact on a macro-economic scale or national security often receive, in our opinion, too little attention from the authorities due to lack of time and the chances of prosecution.
In any case, choose a party that has the expertise and resources to assist in the event of an attack. This often helps to minimize or even completely eliminate the impact. An attacker is less likely to carry out and persist with a DDoS if they know or notice that it yields little or no results.
Do you have further questions? Need assistance? Or are you unsure about the security or DDoS protection of your current environments? Please feel free to contact us!